Instagram System Design Interview: Designing a Scalable Session Management System
bugfree.ai is an advanced AI-powered platform designed to help software engineers master system design and behavioral interviews. Whether you’re preparing for your first interview or aiming to elevate your skills, bugfree.ai provides a robust toolkit tailored to your needs. Key Features:
150+ system design questions: Master challenges across all difficulty levels and problem types, including 30+ object-oriented design and 20+ machine learning design problems. Targeted practice: Sharpen your skills with focused exercises tailored to real-world interview scenarios. In-depth feedback: Get instant, detailed evaluations to refine your approach and level up your solutions. Expert guidance: Dive deep into walkthroughs of all system design solutions like design Twitter, TinyURL, and task schedulers. Learning materials: Access comprehensive guides, cheat sheets, and tutorials to deepen your understanding of system design concepts, from beginner to advanced. AI-powered mock interview: Practice in a realistic interview setting with AI-driven feedback to identify your strengths and areas for improvement.
bugfree.ai goes beyond traditional interview prep tools by combining a vast question library, detailed feedback, and interactive AI simulations. It’s the perfect platform to build confidence, hone your skills, and stand out in today’s competitive job market. Suitable for:
New graduates looking to crack their first system design interview. Experienced engineers seeking advanced practice and fine-tuning of skills. Career changers transitioning into technical roles with a need for structured learning and preparation.
Modern web applications demand secure, fast, and scalable session management systems to support millions of users across devices and platforms.
In this post, we walk through a complete design of a production-ready session management system — covering both functional and non-functional requirements, traffic estimations, API and database design, architecture decisions, trade-offs, and failure scenarios.
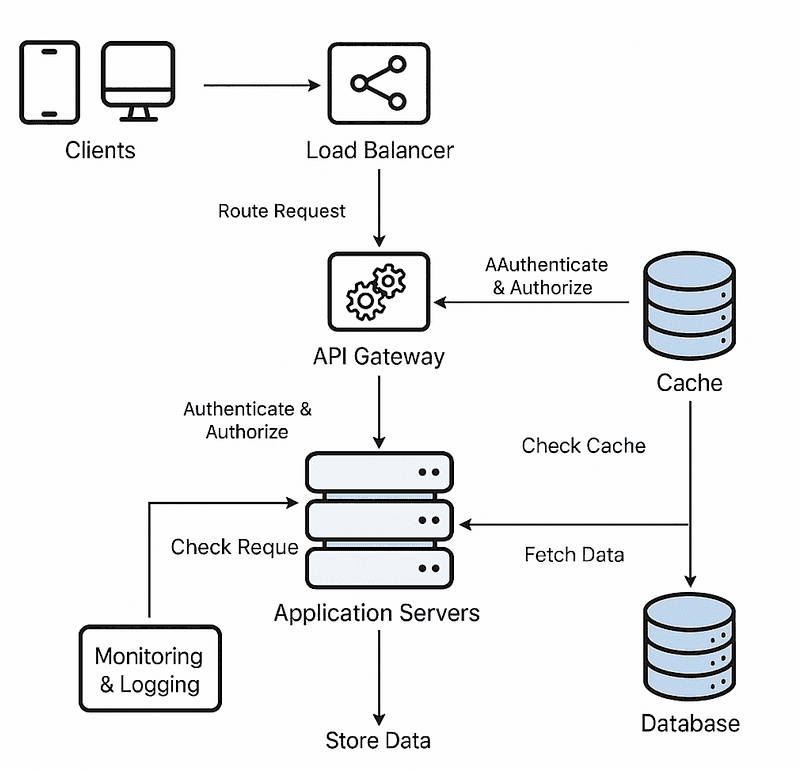
System Design Diagram for Session management service
Functional Requirements
Session Creation
- Initiated on user login.
- Generates a globally unique
sessionIdusing a UUID or cryptographically secure random string. - Persists user-related metadata such as
userId,ipAddress,userAgent,deviceId, and a computed expiration timestamp.
Session Retrieval
- Retrieve session data using
sessionId, primarily for authentication and validation purposes. - Allow listing all active sessions associated with a user, useful for device management or security dashboards.
Session Update
- Extend or reset session expiry to accommodate active usage.
- Modify metadata fields like
lastSeen,geoLocation, or custom flags like MFA status.
Session Deletion
- Explicit deletion triggered by logout or device revocation.
- Automatic TTL-based cleanup when sessions expire.
- Bulk deletion capability for admin or security workflows.
Session Validation
- Used in API request middleware to verify session validity and expiry.
- Cross-check
sessionIdwith cache/database, ensure token freshness.
Concurrency Handling
- Ensure atomicity in session updates, especially with rolling expiry or lastSeen timestamps.
- Use optimistic locking (e.g., versioning or ETags) or distributed locks if needed.
Scalability
- Horizontal scaling for stateless session services.
- Session store and cache should scale independently to handle throughput peaks.
Security
- Session IDs must be cryptographically strong and unpredictable.
- Enforce secure transmission (HTTPS), and encrypt sensitive data at rest.
- Implement protection against session fixation, hijacking, and reuse.
Non-Functional Requirements
- Performance: Average latency below 10ms for reads, <50ms for writes under peak load. Handle 10,000+ RPS.
- Reliability: Service should maintain 99.99% uptime, with regional failover and replication.
- Scalability: Should support elastic horizontal scaling via container orchestration platforms like Kubernetes or ECS.
- Consistency: Eventual consistency acceptable for reads; strong consistency for writes in critical paths.
- Security: Enforce TLS 1.2+, audit logs for session access, token revocation support.
- Resilience: Graceful degradation, retries with exponential backoff, health probes for orchestration.
Traffic Estimation and Data Volume
Assumptions:
- 10 million Daily Active Users (DAUs), each logging in once daily.
- Sessions live for an hour, but average activity window is 30 minutes.
- 10x spike during peak hours (e.g., product launch).
- Session object size is approximately 1 KB.
- Sessions retained for 30 days for audit or analytics.
Write Operations (per day):
- Session creations: 10 million
- Session updates: 2 million
- Session deletions: 10 million (either explicit or TTL-based)
Read Operations (per day):
- Session retrievals: 40 million (e.g., token-based auth middleware)
- Session validations: 40 million (e.g., protected API endpoints)
Storage Requirements:
- 10 GB/day → 300 GB/month raw
- 3x replication = ~900 GB including fault tolerance
- Cached sessions (hotset) estimated at ~500k concurrent sessions during peak
API Design (RESTful)
Create Session
- POST
/sessions - Payload:
{ "userId": "...", "deviceInfo": "...", "ipAddress": "..." } - Response:
{ "sessionId": "...", "expiry": "..." }
Get Session
- GET
/sessions/{sessionId} - Returns full session metadata if active
Update Session
- PUT
/sessions/{sessionId} - Allows mutation of expiry timestamp, additional data
Delete Session
- DELETE
/sessions/{sessionId} - Performs hard delete or marks session as invalid
Validate Session
- GET
/sessions/{sessionId}/validate - Returns
{ "isValid": true/false, "expiry": "..." }
List Sessions by User
- GET
/users/{userId}/sessions - Returns all active sessions for a user
Database Design and Access Pattern
Primary Storage: NoSQL Document DB (MongoDB, DynamoDB)
- Schema-less nature supports evolving session structure.
- Indexed fields:
sessionId(PK),userId,expiry - TTL index on
expiryfor automatic cleanup - Writes are idempotent; conditional updates for race protection
Redis Cache Layer
- Store
sessionId -> minimal session data(e.g., expiry, userId) - TTL in Redis mirrors DB expiry
- LRU eviction, distributed using Redis Cluster or Elasticache
- Cache invalidation on session deletion
Optimization Strategies
- Shard MongoDB by
userIdto balance load - Use batched writes for high-throughput updates
- Backfill analytics store with access logs (e.g., for dashboarding or ML fraud detection)
High-Level Architecture Overview
- API Gateway: Authenticates client tokens, enforces quotas, routes requests
- Load Balancer: Distributes traffic to service replicas
- Session Service: Stateless microservice, implements full session lifecycle
- Redis: Caches active sessions for low-latency validation
- MongoDB/DynamoDB: Durable session storage, indexes, TTL management
- Monitoring: Prometheus, Grafana, alerting pipelines
- CI/CD: Rollbacks, blue/green deployments, integration with auth providers (e.g., Auth0)
Design Trade-offs and Justifications
- SQL vs. NoSQL: SQL offers strong consistency and joins but lacks horizontal scalability for high-write workloads. NoSQL like DynamoDB/MongoDB enables flexible schema and linear scalability, at the cost of complex transactions.
- Caching: In-memory caching (e.g., Redis) drastically improves read latency and offloads database reads, especially for validation. Risk of cache staleness is mitigated with TTLs and write-through patterns.
- Strong vs. Eventual Consistency: Strong consistency is critical during login/logout, but eventual consistency is acceptable for listing sessions or updating metadata like
lastSeen. - Deployment Architecture: Stateless services deployed via Kubernetes or ECS simplify horizontal scaling. Each component is separately autoscaled and monitored.
- Session Token Security: Prefer short-lived tokens with refresh tokens over long-lived sessions. Consider token binding to IP or device fingerprint to reduce hijacking risk.
Fault Tolerance and Failure Scenarios
- Service Failures: Auto-healing pods, health checks, and circuit breakers.
- Data Corruption: Write-ahead logs, daily backups, and alerting on data integrity anomalies.
- Network Partitions: Graceful degradation and retry logic.
- Cache Miss or Eviction: Fallback to DB, pre-warming strategies for login spikes.
- Security Breaches: Token revocation lists, IP throttling, geofencing, anomaly detection pipelines.
- Region-Level Outage: Multi-region failover, global DNS load balancing.
Other Considerations for Session Management
- Use signed, encrypted JWTs with limited lifespan
- Leverage opaque tokens for session IDs (stored in backend only)
- Implement token rotation, idle timeout, and absolute expiry
- Avoid storing sensitive user data in session payloads
- Provide end-user visibility into active sessions with ability to revoke
Final Thoughts
Session management at scale is a foundational system for modern applications and demands a robust design that addresses correctness, security, observability, and efficiency. With a combination of stateless microservices, efficient cache usage, and distributed databases, it is possible to support millions of concurrent users without compromising performance or reliability.
Practice the question and view the entire solution on bugfree.ai: https://bugfree.ai/practice/system-design/session-management

