Audit Logs in Privacy Systems: If You Can’t Prove It, You’re Not Compliant

bugfree.ai is an advanced AI-powered platform designed to help software engineers master system design and behavioral interviews. Whether you’re preparing for your first interview or aiming to elevate your skills, bugfree.ai provides a robust toolkit tailored to your needs. Key Features:
150+ system design questions: Master challenges across all difficulty levels and problem types, including 30+ object-oriented design and 20+ machine learning design problems. Targeted practice: Sharpen your skills with focused exercises tailored to real-world interview scenarios. In-depth feedback: Get instant, detailed evaluations to refine your approach and level up your solutions. Expert guidance: Dive deep into walkthroughs of all system design solutions like design Twitter, TinyURL, and task schedulers. Learning materials: Access comprehensive guides, cheat sheets, and tutorials to deepen your understanding of system design concepts, from beginner to advanced. AI-powered mock interview: Practice in a realistic interview setting with AI-driven feedback to identify your strengths and areas for improvement.
bugfree.ai goes beyond traditional interview prep tools by combining a vast question library, detailed feedback, and interactive AI simulations. It’s the perfect platform to build confidence, hone your skills, and stand out in today’s competitive job market. Suitable for:
New graduates looking to crack their first system design interview. Experienced engineers seeking advanced practice and fine-tuning of skills. Career changers transitioning into technical roles with a need for structured learning and preparation.
Audit Logs in Privacy Systems: If You Can’t Prove It, You’re Not Compliant
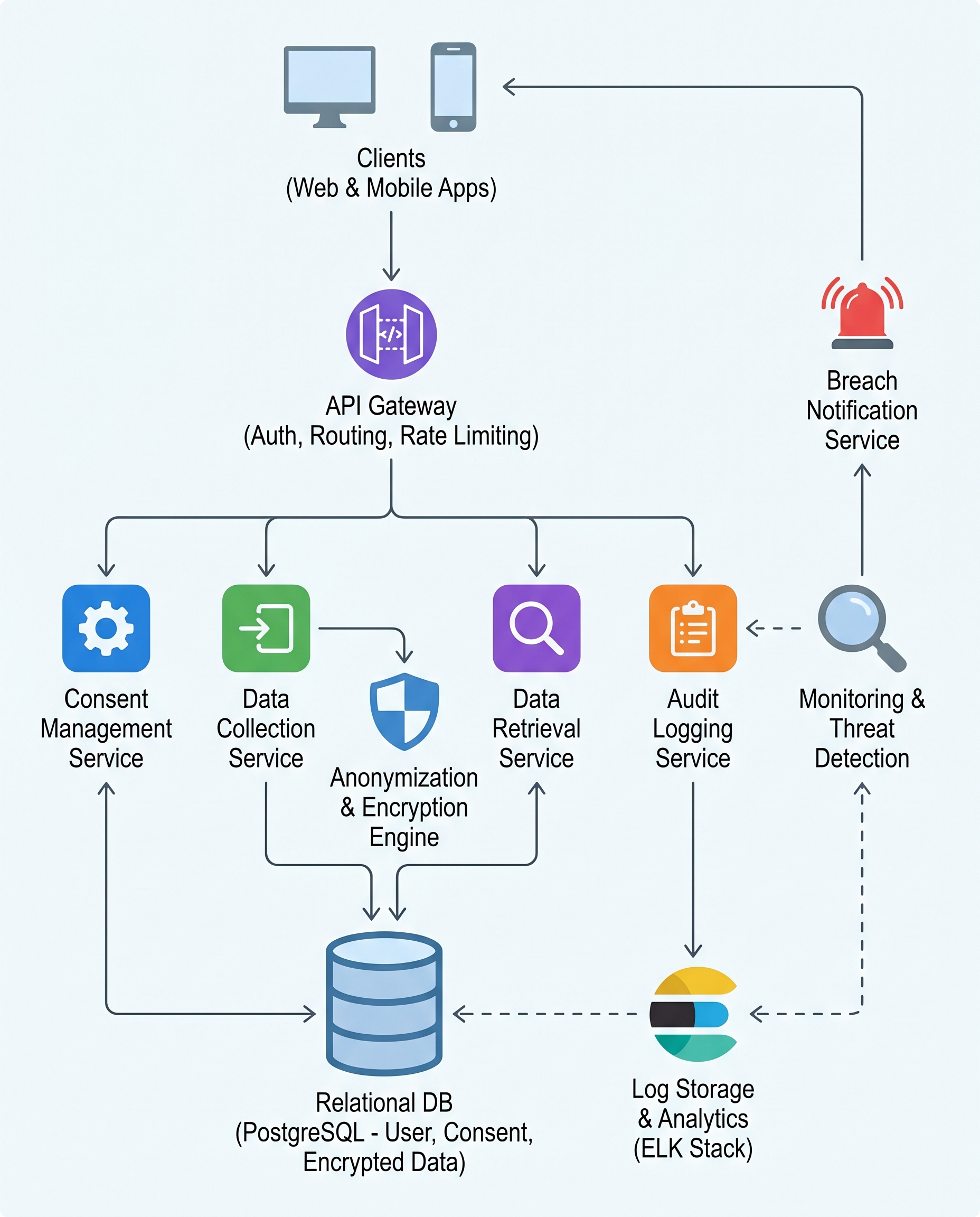
In a data privacy compliance system, audit logging isn’t a nice-to-have feature — it’s the evidence auditors, regulators, and legal teams demand. Every access, change, deletion, and consent update must produce a verifiable, tamper-resistant record describing who did what, when, from where, and why.
Below are practical design principles and implementation patterns to make audit trails reliable, defensible, and operationally useful.
Core requirements: the five Ws (and how to protect them)
- Who: authenticated user ID, service account, or system process
- What: the action and the object (read, update, delete, consent change; resource identifier)
- When: precise timestamp (UTC, monotonic if needed)
- Where: source IP, region, or service origin
- Why: reason, justification, or linked request/ticket ID
Protect these attributes with integrity and access controls so the log itself becomes admissible evidence.
Design it as a dedicated Audit Logging Service
Scattering logs across apps makes them inconsistent and hard to secure. Build a centralized Audit Logging Service that:
- Receives structured events via secure API or agent
- Validates and normalizes schema
- Enforces append-only semantics
- Applies uniform RBAC and access auditing for log readers
- Integrates with SIEM, alerting, and long-term storage
Benefits: consistent format, easier retention management, centralized monitoring, and simpler audit access controls.
Storage and immutability
- Use append-only storage or write-once mechanisms (WORM). Options include:
- S3 with Object Lock / Governance/Compliance mode
- Immutable database / ledger (blockchain or merkle-tree-backed logs)
- Dedicated immutable log systems (e.g., write-once append logs with cryptographic chaining)
- Store checksums and cryptographic signatures for entries. Consider periodic snapshots and publishing root hashes (auditability via hash chaining).
Integrity: cryptographic protections
- Sign log batches or entries using a key on an HSM/KMS
- Hash chains or Merkle trees prevent undetected insertion or reordering
- Track key rotation and keep an audit trail for signing keys
Access control and separation of duties
- Enforce strict RBAC: only authorized roles can read logs, fewer can export
- Use just-in-time access and time-limited credentials for auditors
- Log any access to the audit logs themselves (meta-auditing)
- Maintain separation of duties between system operators and compliance officers
Encryption and transport
- Encrypt logs in transit (TLS) and at rest (KMS-managed keys)
- Protect metadata and payload differently if needed (e.g., redact PII in readable fields, keep full data encrypted)
Retention, deletion, and legal hold
- Define retention policies aligned with regulations and business needs
- Implement automated retention enforcement and safe-delete workflows
- Support legal hold: prevent deletion and preserve chain-of-custody when required
- When deletion is required (e.g., GDPR right to be forgotten), log the deletion event thoroughly—showing that a deletion occurred and that data referenced was removed or irreversibly anonymized
Anomaly detection and monitoring
- Monitor logs for unusual patterns that indicate misuse or compromise, for example:
- Access spikes for a specific record or user
- Access from unusual geolocations or IPs
- Privilege escalation followed by mass reads/deletes
- Rapid successive deletions or consent reversals
- Feed logs into SIEM/UEBA for correlation and automated alerts
Schema and examples
Keep events compact and structured (JSON/Protobuf). Example schema:
{
"timestamp": "2026-05-09T14:32:00Z",
"actor_id": "user:1234",
"actor_type": "user",
"action": "delete",
"resource_type": "profile",
"resource_id": "profile:9876",
"source_ip": "203.0.113.45",
"location": "us-east-1",
"reason": "gdpr_right_to_be_forgotten_request#5432",
"request_id": "req-abc-123",
"signature": "BASE64_SIGNATURE",
"checksum": "SHA256_HEX"
}
Operational best practices
- Index key fields to make audits and forensic queries fast
- Provide secure, audited export for regulators (immutable bundles with signed manifests)
- Test your audit trail during purple-team exercises: simulate malicious deletions or tampering to validate detection
- Automate retention reporting for compliance teams
Interview soundbite
When asked about compliance in interviews, be concise: "Compliance is demonstrated through verifiable, tamper-resistant audit trails. Design a centralized Audit Logging Service with append-only storage, strict RBAC, cryptographic integrity, and anomaly monitoring. If you can’t prove it, you’re not compliant."
Quick checklist
- Centralized Audit Logging Service in place
- Append-only / immutable storage
- Cryptographic signing and hashing
- Strong RBAC and meta-auditing of log access
- Encryption in transit and at rest
- Retention, deletion workflows, and legal hold support
- Anomaly detection and SIEM integration
Audit logs turn system activity into evidence. Treat them as a first-class compliance artifact — not an afterthought.
#DataPrivacy #CyberSecurity #SystemDesign


